TechLetter for starters: ransomware, data transfers, energy information leaks
With security despite encryption
Welcome to the first letter!
Many aspects are still not finalised or not decided. The overarching goal is to structure the content over technology: cybersecurity, privacy, the general technology policy, etc. When relevant, I’ll be annotating stuff with comments/analysis/opinions. I don’t want this to merely be a bunch of links to stories. I imagine aiming at including 0/1-3 items per the categories below in each post, which gives 1-to-9 items on average. Frequency is undecided yet so probably aiming at weekly initially.
Let’s see how this goes. For instance, perhaps even this first edition is already too lengthy! I little experience in newsletters, so balancing should take some while
Security
1)
Very cool technique demonstrating information leaks (via power analysis) allowing to steal things like cryptographic keys (paper, PDF). Power analysis allows to link the small measurable differences in power consumptions with performed operations.
By observing changes in power consumption with a resolution of up to 20 kHz, we show that different executed instructions and features of their operands can be distinguished … We break kernel address space layout randomization (KASLR) from user space
One advised solution:
The RAPL [running average power] interface has a μJ resolution. While reducing the counter’s granularity does not completely mitigate our attacks, the number of traces for some scenarios might become impractical.
While a different domain, back in 2014-2017 we advised similar things with browser-based battery API readout (paper, blog).
2)
Council of European Union is still thinking how to allow lawful access to encrypted content (my analysis). “Security through encryption and security despite encryption”
Words have power. Words may impact policies. Words certainly can change policy and politics. How things are framed matter. Words should be carefully used. Can security be guaranteed despite encryption? In the case of computer/technology security - it cannot be guaranteed without encryption. Such a question makes no sense. But security certainly cannot be guaranteed without strong encryption.
3)
Cyberattack targeting Brazil's Supreme Court of Justice. It disrupted Court’s work ("procedural deadlines were suspended"). This was an interference in the matters of the State . But it is also unclear what's the source of the intrusion. It’s a precedent, anyhow.
4)
Remember the suspicion that a cyberattack (ransomware infection) on German (Dusseldorf) hospital contributed to a tragic death? It seems the German court does not think this is the case.
This was always going to be a battle, says Markus Hartmann, the chief public prosecutor at Cologne public prosecutor's office. After a two-month investigation, Hartmann’s team concluded that there were insufficient grounds to pursue the matter any further. The ransomware was involved in the case but the law means it isn’t possible to blame the hackers with the death.
It was clear that establishing causality would be the most difficult part. In short, the hypothetical was not confirmed. Meanwhile, don’t forget to consider updating your slide decks:


Seems that some cybersecurity policy teams perhaps did not get the memo on time because a few days later (13.11) the communication was phrased along the lines of “In Germany, we recently saw the resulting threat to human health become tragic reality when a woman in Dusseldorf reportedly became the first known death as a result of a cyberattack on a hospital.”. Oh well. Happens.
5)
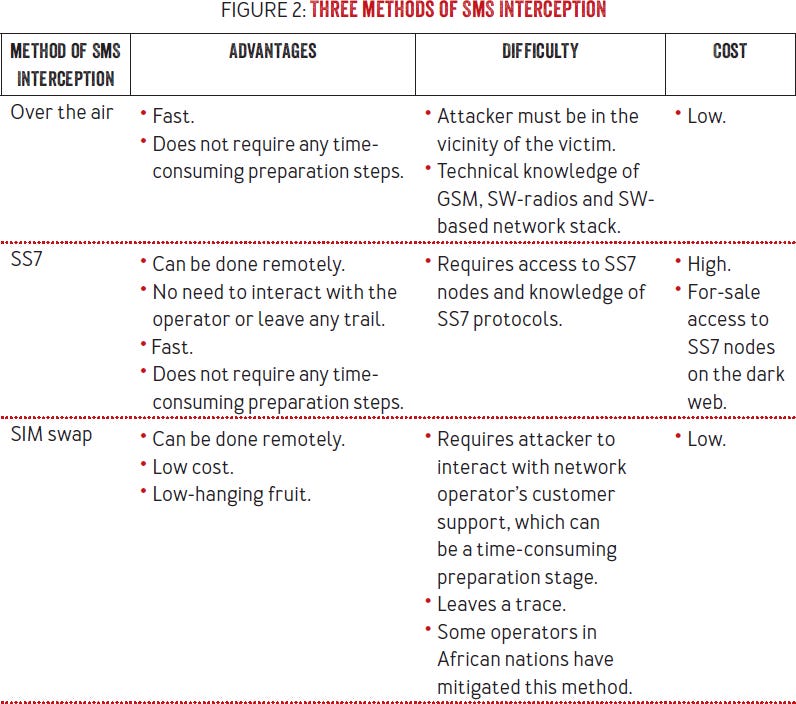
“SMS-based authentication tokens are arguably one of the least secure forms of two-factor authentication. This does not imply, however, that it is an invalid method for securing an online account” (paper).
But for the typical users and use in non-sensitive uses, this is fine. Also, SMS makes it simpler (for the service provider!) to process “forgot password” and other account management aspects.
6)
ICO fined Ticketmaster £1.25million for a 2018 breach with potentially 9.4m of people affected, and confirmed cases of credit card abuse. They were hacked by Magecart in a supply-chain like breach, where the website code infected with skimmers. This is rather a precedent case, and certainly among the most interesting GDPR cases so far. In some ways the software user (Ticketmaster) was fined for using a system with vulnerabilities (supplied from the third-party supplier that got hacked) and the inability of timely detection:
it is relevant that Ticketmaster did not have a method in place to test the security measures between the chat bot and Ticketmaster's own payment page, and a fortiori was unable to identify whether such measures would have been adequate to mitigate the known risks
Privacy
1)
The European Data Protection Board presents a "how to live with invalidated Privacy Shield", about data transfers to third-countries.
Like I said in July, technical approach may be crucial. "keys are reliably managed" is only one such a requirement. To be clear, merely encrypting data is not sufficient. It must be designed well. For example considering the fact that decryption keys should not be available to the third-country actors. Technical, organisational and legal measures may be used. According to the proposed guidelines technical layer will always be important. The proposed guidelines make some things clear.
GDPR requires data localisation in some cases. Especially when the data needs to be used in the clear, unencrypted form
Some data cannot be used in cloud vendors reachable to the jurisdiction of the third-country.
Workers based in the EU and the third-party cannot collaborate “just like that” on some types of data.
It also seems that multi-party computation (MPC) is endorsed:
the processors optionally process the data jointly, e.g. using secure multi-party computation, in a way that no information is revealed to any of them that they do not possess prior to the computation,
That would be grand! MPC is an interesting technology with strong research background, but it is currently rather niche and difficult to deploy in practice. So good luck with actually getting this to use.
3)
British ICO identified the data use practices of the British political parties. "Some political parties (UK) obtained lifestyle-type information on individuals from data broking organisations under commercial agreements". Technologies in political engineering, at a scale. The report is limited to the UK. How it looks in other countries is anyone’s guess. That’s the point, because why would such sources/tools not be used elsewhere? The question is how they are used.
Tech policy
Facebook and Google extended the voluntary bans on political advertising in relation to the US elections. Election silence periods are well known in democracies, though this is mostly related to activities happening few days prior to the election (and/or the day of elections). Lacking such regulations in the US, it seems that the technology actors enforce arbitrary decisions. Talk about stability and predictability. Here’s a nice map how the regulations looks around the world:
That’s it this time, thanks!
In case for some reason you decide to forward this letter further, I’ll leave this thingy below: