TechLetters #149 Israel crisis/conflict cyber-activity. Stealthy cyber espionage tool of unknown origin uses fingerprinting. IT risk companies and their employees due to engagement during wars
Security
Cyberattacks in Israel-Hamas war. While you should not get over-excited with little-to-no impact of the activities that were public, here’s an interesting report of what was visible. You know, the distributed denial of service and stuff like that. But also distributing malicious apps, hijacking alert services. The use of headlined “DDoS bombardment” doesn’t help when there is real bombardment happening. However, expect that what really counts isn’t seen. So it isn’t being covered. https://blog.cloudflare.com/cyber-attacks-in-the-israel-hamas-war/
The Triangulation cyber espionage tool uses outstanding stealth techniques after infection of smartphones. "the victim receives an invisible iMessage attachment with a zero-click exploit". First use of Canvas fingerprinting by malware. How does it work? It draws a pink triangle and checks a "checksum" based on hardware-linked output. This enables the verifiable tracing of a specific device. It is likely stable (impossible to change) - it is permanently identifying a device. The malware is capable to turn on the microphone to record surrounding voices... It can also collect person's device location (GSM/GPS). Attackers "used private undocumented APIs"? Now, who could make such a thing to work?
Supply-chain spillover. Authentication provider 1Password breached (but: no impact). Due to other authentication provider, Octa, breached. Technology is fragile. Hand-waving policy report/advice/requirements on "supply-chain" security are cute, but at the end of the day, a random npm package 0wns stuff.
Inconvenient truth about international humanitarian law qualification of IT/tech companies during wars. Employees of certain IT/tech companies may become unlawful combattants/“legitimate military objectives” (targets for strikes/kills). Whether they are informed about it by their employers is another issue. “when I say “attack,” I mean violence that has the potential to kill, injure, or cause damage, including physical damage. I am not talking solely about cyber responses that have non-physical effects. That is because, when a civilian is engaged in DPH or a piece of company property qualifies as a military objective, IHL does not outright prohibit States from causing kinetic effects against those civilians or properties.” However, since it may be highly inconvenient, maybe better to pretend that we don’t know about this?
Apple will let users verify if the person they speak to over iMessages is really the person, or maybe the account is hijacked. Notifies users when an unexpected security condition occurs. Via implementation of key transparency/verification cryptographic protocol (“Key verification system for end users that provides consistency and privacy for users’ name-to-key bindings, without requiring explicit key management by users”). Contact verification done using Vaudenay's protocol.
Privacy
Every macOS/iPhone (2020+) susceptible to information leak. For example GMail password theft. By visiting a website from Safari/Firefox. CPU architecture attack.
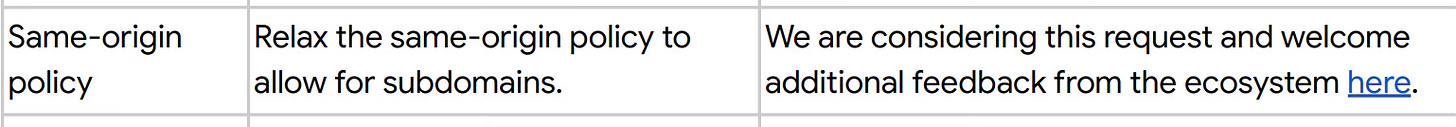
"Privacy Sandbox" testing guide and progress. "Chrome functionality to support this ‘label only’ testing is expected to launch 31 October 2023 and will remain available through the first half of next year". That is a regulatory REQUIREMENT. The problem is that no privacy tests are being announced (perhaps unsurprisingly because CMA is a competition authority). Furthermore, Google Chrome is also considering to relax same-origin policy, cornerstone of web security and privacy. I'd be careful with that! You may add your opinion here.
Technology Policy
Other
During crisis, be careful for misinformation and 'fog of war'. Another example of informational space security and destabilisation. "it was impossible to tell who had caused the explosion or how many people had died ... most reputable names in news media sent push alerts that broadcast Hamas’s claims far and wide". With lack of evidence, nor analysis analysis. Pushing the alerts to hundreds of thousands of readers who get the message instantly, uncritically accepting potential propaganda messages. The effect of the news has tangible political consequences and contributed to destabilisation.
The joys of teaching networking, or CISSP tests. 7-layer OSI model recommendation: "abandon the top three layers, even as categories or analogies. They are complete fiction, anybody teaching them is absolutely wrong". Even better: turn 7-layer model to two-layer model.
In case you feel it's worth it to forward this content further:
Subscribed
If you’d like to share: