TechLetters #70 - Cyberwarfare on Ukraine war, hacked in Russia, 'cyber weapons' producers/users indicted, non-insurance to cyberwar, cookie problems, EU-US data flows, secure PINs
Security
USA says that Russia is considering stepping up cyberattacks on USA. In context of Ukraine war. Previously US intelligence was ... quite accurate. “…It’s part of Russia’s playbook. Today, my Administration is reiterating those warnings based on evolving intelligence that the Russian Government is exploring options for potential cyberattacks…”
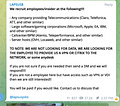
Identity & access management Okta hacked. Data stolen, some evidence leaked. Access systems company... The most interesting key question now is if company customers may be affected (i.e. would it be any easier to enter their systems?) with risks of being hacked. “2.5% (366?) of customers have potentially been impacted ”. The responsible group described here: “extortion campaign against multiple organizations with some seeing evidence of destructive elements”. Many access techniques employed. Including "paying employees" to allow the hacking of the organisation (or their clients, partners, …) they're employed at.
Lots of Russian systems of - apparently - agricultural agencies/companies hacked. System paralysis. Russian designation of the event: "a manifestation of the informational and economic 'total war' that the collective West unleashed against Russia"
Smartphone PIN security. "Using six-digit PINs instead of four-digit PINs provides little to no increase in security and surprisingly may even decrease security"? Well, use alphanumeric PINs. (pdf)
New censorship laws in Russia. Russians spreading “fake news” about state bodies (like military) "operating abroad" (like in Ukraine) face a jail. New censorship law enacted. Fines are Rbs1.5m ($14,250)+ 3 yr jail, or even 10-15 years.
USA is indicting Russian government cyber operators. Of making cyberattacks on critical infrastructure, energy facilities, including (attempts) at nuclear power plants. Formally it's akin of attributing those cyber operations to the Russian State. Including the creation of Triton, dangerous “cyber weapon”-like tool that is able to disable critical infrastructure safety systems. The intention was to gain capability of causing physical destruction, possibly with lethal effects.
Cyberattacks aimed at european charities helping the victims of war in Ukraine. Not good.
North Korea cyber operators use fingerprinting target-hosts before delivering 0day chrome exploits. Here fingerprinting is part of targeting scheme. Targeted specific users of Chrome, Safari, Firefox web browsers.
Insurance from cyberwar? Insurance may not cover potential losses due to cyberwar. It depends on many factors, for example where the target is based.
Privacy
Almost all tested websites may have problems with cookie consent/compliance. Automatic test. Implications for EU regulations: GDPR, ePrivacy.
Trans-Atlantic Data Privacy Framework, US-EU data transfers. "United States has committed to implement new safeguards to ensure that signals intelligence activities are necessary and proportionate" and respect EU data protection.
Technology Policy
Other
In case you feel it's worth it to forward this content further:
If you’d like to share: