TechLetters #71 - Cyber operations vs humanitarian organisations. Cyberwarfare on Ukraine (vs SATCOM, weapons systems). Russia wants to hold liable people making cyberattacks. Spring vulnerability
Today with expanded analysis in the cyberwarfare parts.
Security
Misinformation campaign against International Committe of the Red Cross activities in relation to Ukraine war. Would be nice to learn more. "This misinformation is also putting at risk Red Cross staff and volunteers on the ground and could jeopardize our access to people in need of urgent aid". That said, ICRC had some problems with structuring their crisis response & appropriate wartime information operation. This is quite curious because you’d expect the ICRC to have the proper awareness and skills.
Cyber operations against humanitarian organisations. The ICRC warns from the risks of cyberattacks on humanitarian organisations. "We urgently call on you, the States, to reaffirm that humanitarian organizations, their staff, and humanitarian data must never be targeted, be it in the physical or in the digital world". This was mentioned during the United Nations Open Ended Working Group on information/cyber security. It is curious that there was apparently no linkage at all to the cyberwarfare effects/consequences during war on Ukraine. This is very weird, because the ICRC should should be very focused on cyber operations during armed conflict. Apparently, they are not (or they withhold action, for some reasons, hopefully well-considered).
More details about a cyberattack on SATCOM provider viasat. Very good description, likely a cyberwarfare measure linked to Ukraine armed conflict. AcidRain tool (‘malware designed to wipe modems and routers’) used? That would be the most significant publicly known cyber operation during this war (so far, we will learn more eventually - be sure of that - many events are under wraps).
Amazon says that they are aware of cyber operations targeting humanitarian organisations. "specifically targeted at in order to spread confusion and cause disruption". The ugly face of cyberwarfare.
Hacker group claims they allegedly found ways to disrupt navigation systems for Russian field units. "Lost Russian forces are easier to find and target than ones that know where they are going". They seek to "disrupt artillery fire". “Currently, the group is looking for ways to disrupt artillery fire, at least from systems that employ precision guidance systems. The member said the group has identified several computer servers linked to Russian rockets.” None of this is verifiable. Cyberattacks on weapons systems would be unprecedented (my take here). This also likely would make someone a participant in an armed conflict (with consequences due to a potential military response).
Pentagon would like $11.3bn for cybersecurity. Just for 2023. That’s a lot, considering that figure to entire army budgets in other countries. It seems to be unrelated to Ukraine war. For that, maybe we’d need to wait for another year.
Russian FSB/GRU allegedly hacked Hungarian Ministry of Foreign Affairs. Seems that it allowed full access to data, including classified stuff. For many years. Not the brightest Hungary’s moments. It seems that at some point there may be some concerning information emerging from the European Commission, too.
Russia will seek to bring liable those involved in “cyber aggression” “against then”. Sounds serious. But note the language: “an army of cyber mercenaries, which pursue concrete combat tasks that border on terrorism, is waging a war against Russia.". So, “combat tasks”? They say as if those people were involved in an armed conflict. The official statement is here: “…No one should have any doubts: the cyber aggression unleashed against Russia will lead to grave consequences for its instigators and perpetrators. The sources of the attacks will be identified, the attackers will inevitably be held accountable for their deeds in accordance with the requirements of the law”. It is unclear how they’d want to enforce the Russian law against people based in other countries. Unless they speak of international law (doing whatever), or even laws of armed conflict (i.e. designating the participants as military targets)?
Effects of the cyberattack on satellite communication provider are still there. "did impact several thousand customers located in Ukraine and tens of thousands of other fixed broadband customers across Europe". Seems that the target could be Ukraine. Report here. Does this smell like cyberwarfare?
Around the same time, Viasat and Skylogic began to observe a gradual decline in the number of modems online in the same commercial-oriented partition. This gradual decline of connected modems continued until approximately 0415 UTC, when Viasat and Skylogic observed larger numbers of modems across much of Europe exiting the network over the course of about 45 minutes. All of these modems are serviced by the same consumer-oriented service partition.
Ultimately, tens of thousands of modems that were previously online and active dropped off the network, and these modems were not observed attempting to re-enter the network. The attack impacted a majority of the previously active modems within Ukraine, and a substantial number of additional modems in other parts of Europe.
Subsequent investigation and forensic analysis identified a ground-based network intrusion by an attacker exploiting a misconfiguration in a VPN appliance to gain remote access to the trusted management segment of the KA-SAT network. The attacker moved laterally through this trusted management network to a specific network segment used to manage and operate the network, and then used this network access to execute legitimate, targeted management commands on a large number of residential modems simultaneously. Specifically, these destructive commands overwrote key data in flash memory on the modems, rendering the modems unable to access the network, but not permanently unusable.
Security vulnerability in Spring. Remote code execution in a popular Java framework, used in many places.
No Cyber Pearl Harbors. GCHQ chief has a point "Whilst some people look for cyber ‘Pearl Harbours’, it was never our understanding that a catastrophic cyber-attack was central to Russian’s use of offensive cyber". Forget about useless scenarios of cyberattacks.
Privacy
Google's Privacy Sandbox will test ad attribution and privacy-respective ad targeting. Building privacy-proofed ad infrastructure is challenging. Plenty of things to solve still remain. Not only on Google's part, but also publishers, other companies in the ecosystems.
Technology Policy
Content moderation rules effectively removing evidences of war crimes? Unexpected effect of chasing content rules, disinformation craze over the previous years, and technology. US and Chinese platforms and their policies are the culprit, and the effects of such removals may be problematic. I'm afraid that this is not adequately considered by EU legal acts like the Digital Services Act. Was it difficult to consider? A hot potato? Or?
Other
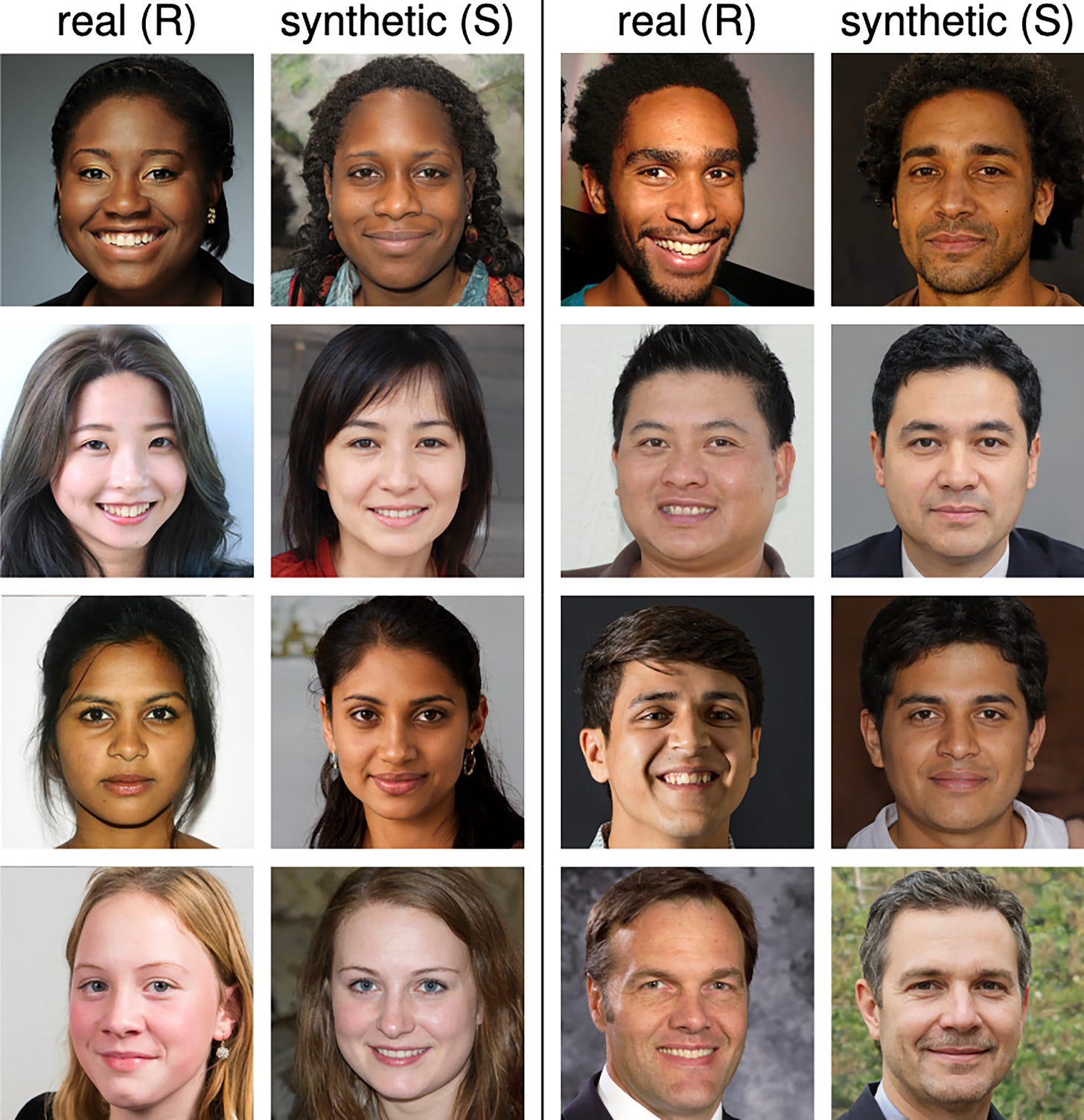
Manual detection of fake/synthetic, AI-generated photos of people is becoming too difficult for humans. Fake photos will be indistinguishable from real ones? Around 48% chance of detection (so roughly random).
In case you feel it's worth it to forward this content further:
If you’d like to share: