TechLetters ☕️ Agentic tools take of FOR ALL and act for you and in between. Malicious AI dev skills spread. Poland grid cyberattacks went destructive. London councils hacked.
OpenClaw is designed to perform actions in the system and services (files, browser, terminal, calendars, instant messengers), so a configuration error or prompt injection vulnerability can translate into real actions on user accounts and data. OpenClaw has grown extremely quickly, which increases the pressure to deploy it without careful consideration, even in corporate environments. Some people connect company resources to it...
Security
My writeup about malicious AI coding assistant skills. Malicious skills targeting Claude Code and Moltbot published to ClawHub and GitHub. Deliver information-stealing malware to macOS and Windows systems.
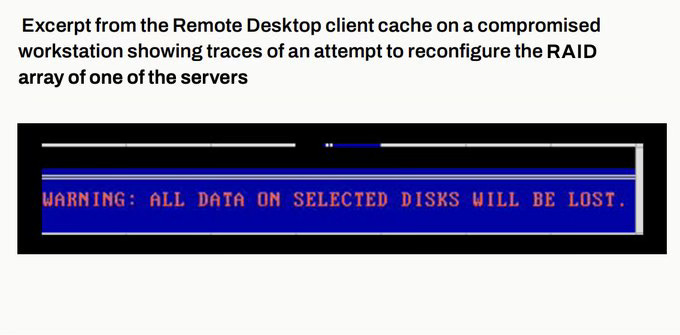
What really happened with cyberattacks on Poland’s power grids. No FUD. “The attacks targeted numerous wind and solar farms, a private company in the manufacturing sector, and a combined heat and power (CHP) plant supplying heat to nearly half a mil‑ lion customers in Poland. All of the attacks were purely destructive in nature“. Due to the destructive actions carried out by the attacker, it was not possible to recover complete logs from any of the compromised devices. In addition to attempts to destroy data on the workstations belonging to the compromised organization, the attacker also attempted to directly destroy data on disks attached to servers within the infrastructure. https://cert.pl/uploads/docs/CERT_Polska_Energy_Sector_Incident_Report_2025.pdf
Suspected Pakistan-linked cyber operator targeting Indian government via spearphish PDFs to geo-fenced ISO delivery (servers hosting the payload only respond to IP addresses in India, with a Windows platform User-Agent). https://www.zscaler.com/blogs/security-research/apt-attacks-target-indian-government-using-gogitter-gitshellpad-and-goshell
Cyberattack (targeted) on Westminster and Kensington & Chelsea councils threatens disruption of London home sales. Searches halted, emergency plans activated, backlog mounting. Shared IT hit. Systems taken down. Data was stolen/exfiltrated. https://www.bloomberg.com/news/articles/2026-01-27/london-cyber-attack-threatens-to-hold-up-thousands-of-home-sales
Privacy
Test-development version of a GDPR Register of Processing done the simple and sufficient way. Extendable, and possible to fully automate the workflow and all the pipelines (I did not set it up on my server yet). https://github.com/lknik/GDPR-RoPA
Technology Policy
Cyberspace has become an arena for competition, contestation and sometimes even uninhibited confrontation, mirroring geopolitical tensions and international rivalries.
The new French cybersecurity strategy moves from guidance and resilience toward operational measures that can make a change at a scale. It however leaves escalation triggers and foreign information manipulation procedures undefined.
Main points
It proposes a “cybersecurity filter for the general public” that would block access to malicious sites. It is undefined how this would work (network perimeter?) or how exactly would “malicious” be defined. Would it be a banned website register? It would not be censorship if it was limited to verifiable malicious infrastructure and governed by a clear legal basis, transparent criteria, independent oversight. Going beyond that could become contentious. But there are no indications of going beyond infrastructure/cyber aspects. Disinformation and foreign information manipulation are not mentioned. Information manipulation is barely mentioned in a footnote.
Deterrence is framed as coordinated use of judicial, technical, diplomatic, military, and economic tools, and it includes offensive cyber capabilities. Public attribution is listed as an option to be put to political authorities. It enables coalition response, sanctions pathways, and public messaging.
Internationally, it states it will contribute to establishing a UN Global Cybersecurity Mechanism by 2026 to operationalise the standards of responsible behaviour agreed at the UN in 2015. The text does not use the term “cyber norms”. Is it the cyber norm terminology on the way out?
Naturally, the strategy puts an emphasis on European autonomy.
Other
The new Austrian Risk Picture argues that hostile actors, especially Russia, use hybrid influence by treating the information space as an operational domain. The goal is to undermine (or destroy?) the European Union. In response, it calls for information sovereignty, continuous monitoring and analysis of online information, and targeted strategic communication as part of national resilience. https://verteidigungspolitik.at/risikobild
In case you feel it's worth it to forward this content further:
Subscribed
If you’d like to share: